SAML - FotoWeb attribute mapping
Where to configure: From the Tools menu (cogwheel icon) go to Site Configuration > Security > Single Sign-on.
When setting up FotoWeb with SAML SSO, you can define attributes on the Identity Provider (IdP) that are synchronized to FotoWeb when a user is imported.
Such attributes can, for instance, include:
- Group membership
- Address information mapped to corresponding FotoWeb user information fields
- User initials
- Phone numbers, and so on.
Tip: The Managing Groups using SAML topic explains how to transfer group membership, with an example using ADFS. However, the procedure for doing so is quite similar whether using ADFS or another provider.
Default properties in FotoWeb
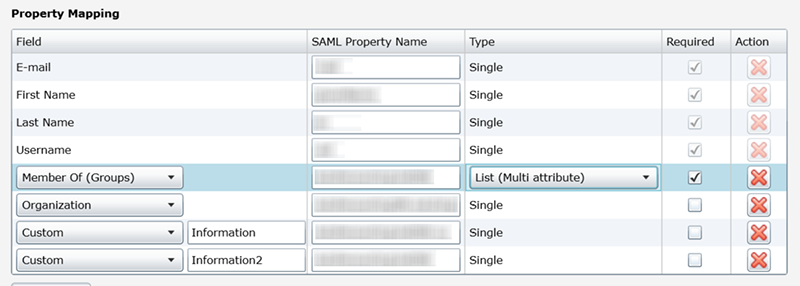
Four properties are default and required when integrating FotoWeb with an IdP using SAML:
E-mail, First Name, Last Name and Username.
The names of these properties can be changed in FotoWeb to accommodate, for example, an IdP that cannot modify the name of its outgoing attributes for the corresponding fields.
Example: If the IdP always sends the username as an attribute named uid, change the FotoWeb SAML Property Name for Username to uid to match that of the IdP. Remember that SAML property names may be case sensitive.
Tip: The SAML Property Name seen above is often referred to as SAML Attribute Name in many IdP setups.
Additional attributes can also be set as required as needed. When an attribute is required, a user will not be able to log in if the identity provider does not set the attribute.
Synchronizing additional properties
Additional properties synchronized via SAML can be mapped to FotoWeb user information fields. Choose the FotoWeb field using the drop-down list and enter the corresponding SAML attribute that the IdP delivers.
Attributes with multiple values
When setting up attributes, IdP's have different ways to transfer attributes with multiple values. FotoWeb supports multiple values for group memberships and address information, attributes that often comprise more than a single value.
For example, an IdP may transfer group membership as a single attribute that translates to a single SAML property mapping in FotoWeb - this 1-1 relationship means that a single group in the IdP translates to a single group in FotoWeb associated with the SAML property.
However, it's more typical for an IdP to transfer multiple group memberships. These can be transferred as a comma or semicolon-separated list, or as an array. You can set the format of the attribute's values in the Type column (see the example screenshot above), and choose between Single (1-1 mapping) or List, where you can choose between comma separation, semicolon separation, or Multi, meaning an array.
Group membership mapping
To synchronize groups from the IdP to FotoWeb, choose the Member of (Groups) entry from the FotoWeb user information field drop drop-down list then enter the corresponding SAML attribute it should be mapped to. With an ADFS integration, the default name of the SAML attribute is groups, but different IdPs may use different attribute names.
Next, choose the format of the group membership values from the IdP, Single, or List.
Important distinction: While the group mapping described above refers to linked groups, it's also possible to create default groups in FotoWeb in which all users who are imported via SAML are placed. Since having default groups means that anyone who authenticates via SAML can access FotoWeb, we recommend disabling all default groups if you're enforcing strict access control to FotoWeb.
Address mapping
An address information attribute from the IdP can also contain multiple values. By choosing List as the type, each attribute value will be added as an individual street address line.
Important points to note
- When the IdP sends an attribute, that attribute is always updated when a user logs in via SAML.
- If there is no SAML attribute mapping to a FotoWeb field or custom property, or if the attribute is not required and the IdP does not send it, then any existing Fotoware user data is not overwritten. This allows additional user data to be entered in the Fotoware user management module, for example, without risking it being overwritten.
