Setting up SSO with Microsoft Entra ID
Microsoft Entra ID integration
Note: Microsoft ended support for Azure Active Directory Authentication Library (ADAL) in June 2023.
All 8.0 versions of FotoWeb On-Premises use the Azure Active Directory Authentication Library (ADAL) for Single Sign-on (SSO) with Microsoft Entra ID. FotoWeb 8.1 uses the newer Microsoft Authentication Library (MSAL) and is therefore supported by Microsoft. For security reasons and to ensure that SSO will continue to work, we recommend that all customers using FotoWeb On-Premises 8.0 and SSO with Microsoft Entra ID update to the FotoWeb version 8.1.
Microsoft Entra ID (formerly Azure Active Directory) integration supports organizational accounts as well as personal Microsoft accounts. Access control and assignment of groups and user licenses are either group-based or role-based access control.
Tip: The Microsoft Entra ID integration uses the Open ID Connect protocol and is recommended because it is the easiest to set up. If more advanced customization is required or additional user information needs to be imported from the directory, you can use SAML with Microsoft Entra ID.
The following user properties are imported from the directory. Currently, these cannot be configured, and all of these fields must have values:
- Username
- First name
- Last name
- Email address
Prerequisite
Connecting clients to Microsoft Entra ID requires a secure connection, so Fotoware must be configured with TLS (HTTPS) and a trusted certificate. For more information, see Configuring Fotoware for secure connections.
Configuring SSO with Microsoft Entra ID
Adding the Fotoware application to the Azure portal
- Log in to the Azure portal and open Microsoft Entra ID.
- Select Add > App registration.
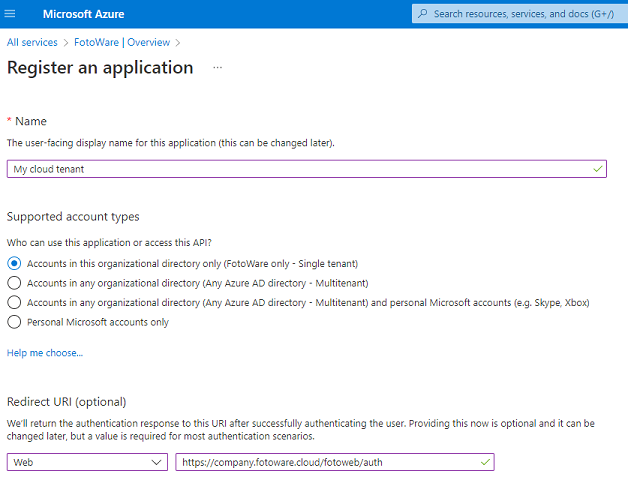
- Enter a name for the application.
- Select Web from the Select a platform drop-down list.
- Select the Redirect URI that your application uses. For single sign-on to a Fotoware site, the URL must have the following format:
https://<site hostname>/fotoweb/auth/signin-oidc
Example: https://contoso.fotoware.cloud/fotoweb/auth/signin-oidc
Alternatively, you can copy the URI (https://internalpreview.fotoware.cloud/fotoweb/auth/signin-oidc) from the Single Sign-on settings for the site. (Go to Site Configuration > Security > Single Sign-on).
- Select Register.
Tip: After creating the application registration, open the Overview section for your newly registered application to retrieve the Application ID (see the example below). You need this ID for the Fotoware Microsoft Entra ID configuration in the site configuration later.
Note: If you previously enabled implicit grant for ID tokens (in the Authentication section) for Fotoware 8.0, we recommend that you disable this option for Fotoware 8.1.
Assigning permissions to the application
- Open the API permissions view for your application and select Add a permission.
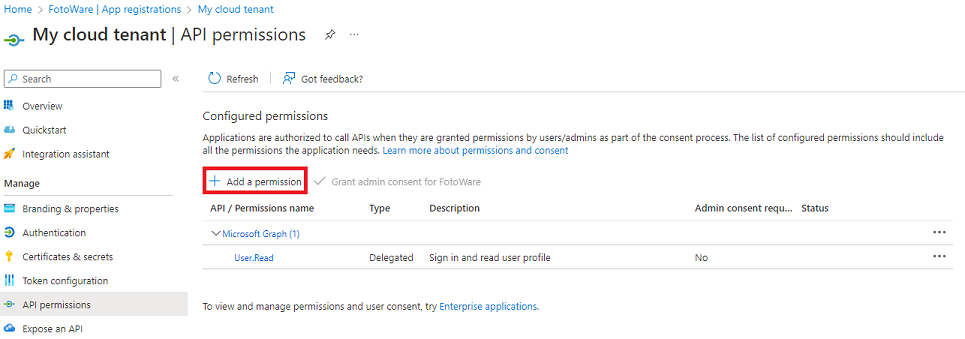
- Use Microsoft Graph and add the User.Read Delegated permission.
When using group-based access control, you need to add access the directory as the signed-in user (Directory.AccessAsUser.All). This is not necessary if you are only using role-based access control.
- Select Save to update the permissions.
Creating the application secret
- Open the Certificates & secrets view for your application. You find this in the same menu as API permissions above or as a link in the Overview section.
- Select New client secret.
- Enter a description (simply a label) in the Description field.
- Select a duration from the Expires drop-down list. For security reasons, a key can be valid for a maximum of two years.
- Select Add to create the client secret. You can then copy it to the clipboard and paste it into the Application key field in the Microsoft Entra ID settings in the Operations Center.
Note: It is the customer's responsibility to replace the application key before it expires. Because the validity of application keys varies, it's practical to set a reminder in your maintenance calendar to replace the key before it expires. If the key does expire, users will temporarily lose access to the system.
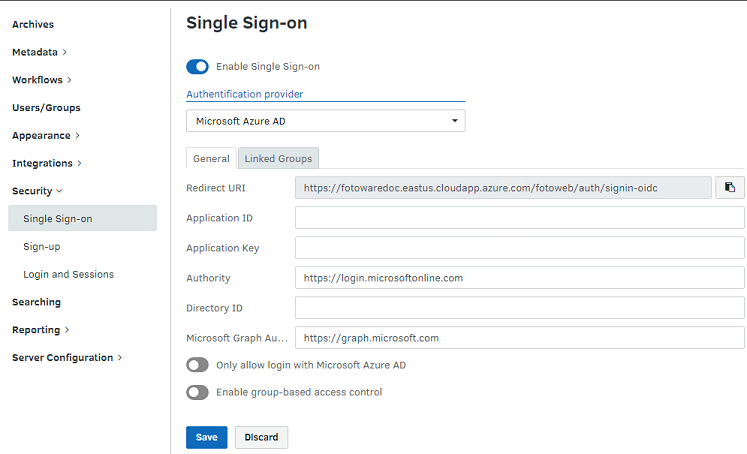
Adding Microsoft Entra ID information to the Fotoware Site Configuration
Make sure you have the necessary information from the Azure portal before proceeding:
Application Id - You can find this in the Overview section.
Application Key - The secret generated in the Azure portal.
Authority - This is the URL of the Microsoft Entra ID authentication service. Typically, it is https://login.microsoftonline.com (the global Microsoft Entra ID service), but this can be different when using different authentication providers.
Directory ID - You can find the Directory ID in the Overview section, next to the Application ID.
Microsoft Graph Authority - This is the base URL for Microsoft Graph, used for retrieving user and group information.
Adding the information to the Fotoware tenant in FotoWeb Settings
- In the FotoWeb Settings app, open Sites.
- Select Configuration for the site in question.
- Go to Security > Single Sign-on.
- Turn on the Enable Single Sign-on toggle.
- Enter the Application ID, Application Key (called Client Secret in the Azure portal), and Directory Id values and save the changes.
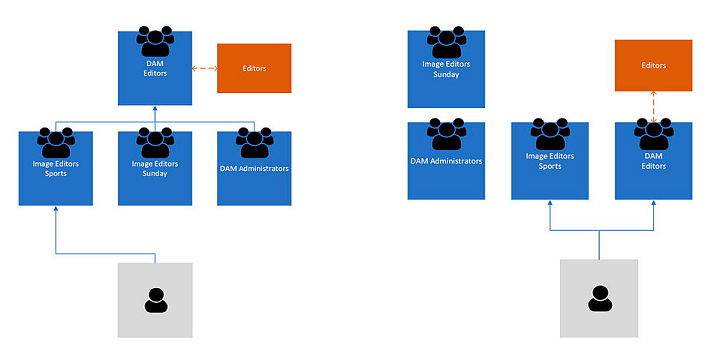
Groups and access control for Microsoft Entra ID
Next, you need to import groups from thMicrosoft Entra ID to give them access to Fotoware. You can then assign access to Fotoware archives and actions using the imported groups.
